Microsoft are forcing, as of the 15th September 2023, Authenticator apps over text and voice authentication to improve security.
Here is some help on how to get the APP installed and running on your mobile device.
Category: Training & Support
How secure is my password and how long will it take to crack?
This topic comes up quite a fair bit some some clients. They do not realise the risk of having simple passwords until it’s too late.
It also means people can be looking at your data without even knowing.
We recommend passwords at a minimim to be 6 characters (however we recommend 8) , and also to have upper, lower, alphanumber and special characters in the password.
The password %^@gtgTT is easier to crack than aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa
The reason is only because of length not complexity.
Here is some examples of weak passwords used in 2015.
To see how hard it is to crack your password, click this link and it will take you external to our site using a calculator to see how long it takes.
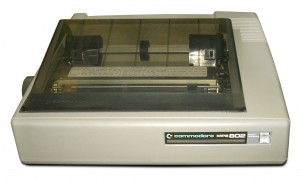
How to make printer default in terminal server ( TS ) / remote desktop server ( RDS )
If you are wanting to use your printer on a Terminal Server (TS) or Remote Desktop Server (RDS), ensure you have allowed your connection to redirect your printers or they will not been seen on the remote server.
To set your remote session default printer, please ensure that if you want a local printer to be the default printer on the server, it must be set to the DEFAULT printer on your computer.
To select a default printer
-
Open Devices and Printers by clicking the Start button
, and then, on the Start menu, clicking Devices and Printers.
-
Right-click the printer you want to use, and then click Set as default printer. (You’ll see a check mark on the printer’s icon signifying that it’s now your default printer.)
If you are running a Thin Client device, you will need to either have a VPN setup or the printer needs to have its port and IP address open to the internet.
Setting default printers on Thin clients, (unless there is an OS or is capable of seeing the local printer in its OS), is a little more complex and not discussed here.
If you still need assistance, please contact Sterling IT via our contact form or call our office.
Received an email? Do you click or not click? – Malware, Scams, Trojans, Viruses could be lurking
The internet has become an indispensable tool for everyday life, both personal and business. Its global use and familiarity has also opened the doors for cyber-criminals to take every opportunity to exploit vulnerable people through disturbing online attacks. Online scams and malware are also becoming increasingly sophisticated, and while IT professionals are aware of what to look for and how to fix problems when they arise, their colleagues may be confused by the latest scams discussed in the media.
Botnets
A botnet is the result of a criminal using malware (malicious software) to turn a computer into a bot, short for robot. In conjunction with a large number of other computers, these systems together form a botnet. Bots can often propagate themselves across the Internet by searching for vulnerable and unprotected computers. Exposed computers can be infected quickly and unknown to the user stay dormant until they are required to perform their detrimental attack. Once infected these bots can be controlled remotely to perform automated tasks over the internet such as sending out spam, malware and spyware; launching denial of service (DoS) attacks against other systems; or participating in other types of cyber-crime such as theft or fraud.
Hacking
Computer hacking has been around much longer then people have had PCs in their own homes, and is the term used to describe gaining unauthorised access into a computer. Hacking can be used to find weaknesses in your security settings which are then exploited to gain sensitive or personal information, to install malware, or to block or hijack your access to websites or email.
Malware
Extremely common, malware, or malicious software, is software you don’t want to infect your computer. Malware includes computer viruses, worms, ransomware and Trojan horses. Specifically designed to disrupt, damage or gain control of a computer system or data, therein each of these types of malware has its own purpose. Malware does a range of things, it may tell you that your computer has a security problem, re-formats your hard drive, alters, deletes or encrypts files; steals sensitive information, sends unauthorised emails, or takes control of your computer and all of the software on it.
Types of Malware
Viruses
A computer virus when executed will replicate by inserting copies of itself (possibly modified) into your computer programs, data files, the hard drive or connected network shares. By doing this the virus infects your system and interferes with the way a computer operates. Viruses are often spread via normal looking attachments in an email message or instant message; through downloads, or in pirated software.
Trojan Horse
Like the Greek tale, the Trojan horse or Trojan, employs social engineering so that it looks legitimate, useful or interesting to the potential victim who is then more susceptible to installing it on their computer. As a non-self-replicating type of malware program it is designed so when it is executed it carries out the actions determined in the program, often including joining the computer to a botnet.
Ransomware
As a relatively recent addition to the malware family, ransomware is a digital form of extortion. When you open a malicious email attachment or click a malicious link in an email message, instant message, on a social networking site, or other website; ransomware is downloaded onto your computer and is designed to block access to all your files and programs until a sum of money is paid. A computer becomes basically inoperable as you have no access to any of your files (unless you have done regular data backups). It is generally advised that you don’t pay the ransom as you cannot be guaranteed you will get the key or code to unlock your files.
Phishing
Phishing has also become a firm favourite of cyber-criminals. These sophisticated modern day forgers use deception and social engineering techniques to trick users. This is done by sending emails, text messages or website links purporting to be from authentic companies that the victim may have had previous communications with (also called spoofing). These fake messages or links are then used to persuade the recipient to reveal personal information including usernames, passwords and credit card details. Phishing scams have become increasingly prevalent because they are easy to execute, and with little effort.
Spam
Spam is another common method for sending information out and collecting it from unsuspecting people. Spam is usually the mass distribution of unsolicited messages, marketing, advertising or pornography. Spam tends to annoy people mostly by clogging their inboxes with junk, however it can also be a vehicle for malware, scams, fraud and threats to privacy.
TIPS FOR CYBER SECURITY
It is vital that anyone who sends and receives emails daily (at home or at work) is made aware and well educated on these common types of cyber threats.
There are a wide range of things you should remember or put into place within your organisation, to ensure your computer/computers are protected the best way possible.
• Avoid giving your email address out online. If you publish your email address on the web, make it unscannable so that it cannot be harvested by bots. There are alternative ways to display an email address which in turn makes it hard for spambots and cyber criminals to harvest it.
• Never open an attachment that is a .zip file or .exe file unless you are expecting it. Files from unknown senders often contain some kind of malware or virus.
• Check who is sending you email communication. Be aware that malware, phishing scams or spam may come from unrecognisable or odd email addresses, however legitimate email addresses can be forged easily.
• Never respond. If unsure, report the message as ‘spam’ to your service provider, and delete it! Also, you should delete the email from your trash to save you accidentally opening it in the future.
• Only click links from trusted senders. If an email has a link you don’t recognise, take a closer look by hovering your mouse over and checking the destination in your browser. If it doesn’t match, it is not legitimate.
• Check for spelling, grammar and syntax. Most malware, phishing scams or spam originate from foreign countries so may contain some very obvious errors.
• A reputable company or organisation will never use an email to request personal information. If you think there is a possibility it may be legitimate, type the real URL into your browser or contact the company directly.
• Reading an email in plain text rather than html can help to avoid phishing attempts, however this is not 100% foolproof.
• Report any suspicious or scam emails to the company that is being imitated, your email security provider, or to SCAMwatch.
• If a computer runs slowly, keeps crashing or stops responding often, this could be a sign that the computer is infected. Get an IT professional to take a look for you.
• It is extremely important to back up your data every single day.
• Utilise multilayered defences. This includes installing anti-virus, anti-malware, anti-spyware, and using cloud based email filtering and web filtering services. You should also not conduct day to day work with Administrator privileges on your workstation. Instead, you should use elevated privileges only when required, for example to install trusted software. Having one form of protection alone may not cover you for all the possible threats.
• Keep your software regularly updated. Software that updates automatically is incredibly beneficial to busy organisations.
• Use strong passwords and keep them secret. It is also a good idea to change them on a regular basis. Don’t use the same password for multiple accounts.
• Install a firewall on your computer and never turn it off.
• Increase security settings on your browser. You can limit user rights to certain online sites.
• Use external devices cautiously. This includes USBs and iPads/iPhones etc. as these can become infected with malware, corrupting your computer.
Cyber criminals are quite adept at tricking email users into falling for their scams. They are always coming up with new methods of deception. It is in the best interest of every company to ensure all their employees are educated on the most commonly known threats. Staying cyber-vigilant and applying solid security measures, is always the best defence against any future breaches.
Want to add another of level of protection on your email? Filter with Mailguard – the providers of the information above.
Need more information, quote on Mailguard or training for your staff?
Contact Us NOW! – Don’t Delay
What is a DDoS ?
We found this video which simply explains what a DDoS attack is.
It also shows how cheap you cab buy a DDoS attack and how they work.
Watch the video and if you need more information, please contact Sterling IT
Cryptolocker attack but removed and all data recovered with zero data loss
Attack of one of the worst Trojans around.
Last week, for the very first time, one of Sterling IT’s customers was attacked with Cryptolocker virus.
When we had the alert, and then found client couldn’t access files, we thought it was just a corruption. Upon inspection, most files were renamed with .encrypted at the end and a HTML file explaining to pay a ransom to recover all the emails.
Sterling IT went into Disaster Recovery Mode (SITDR) and we were able to save the client from any data loss (even though EVERY file on 1x user PC plus most shares on the server were affected, as this user was in management and accounts security groups and shares). Using Shadow Protect and our monitoring systems, we were able to lock down the network, recover all files from DR backups and get the client back up and running.
It was first noticed because of Dropbox. As this company uses Dropbox for some business applications, and the infected user also had Dropbox access, ALL FILES were deleted. The only savior was one of the PCs was locally backed up which the files were recovered from there. (we recommend using private sharing apps with Synology , synocloud, rather than Dropbox as you have full control and is PRIVATE CLOUD).
How did this all happen?
Simple, opening an email with the Trojan. You might also ask about protection mechanisms we have.
First and foremost, the client recently moved to Microsoft Office 365. We would have thought that Microsoft anti-spam and antivirus would have maybe picked this up as first defense, but obviously didn’t. The second defense was a Fortigate firewall with antivirus scanning – been a great defense in general. And thirdly, antivirus and firewall on desktop.
Even with ALL these defenses, the Trojan still go through.
We have many clients sending us emails daily asking IS THIS SAFE? This is what we are here for, to help and protect our clients. Its FREE and QUICK!



 , and then, on the Start menu, clicking
, and then, on the Start menu, clicking